GDPR Compliance for eCommerce: Key Steps
If your Australian eCommerce business interacts with EU customers, GDPR compliance is mandatory. Whether you’re shipping products, collecting data, or tracking behaviour, these rules apply to you. Failure to comply can result in fines of up to €20 million or 4% of global revenue - whichever is higher - and damage your reputation.
Here’s what you need to know:
Who needs to comply? Any business processing personal data of EU residents, even if based outside the EU.
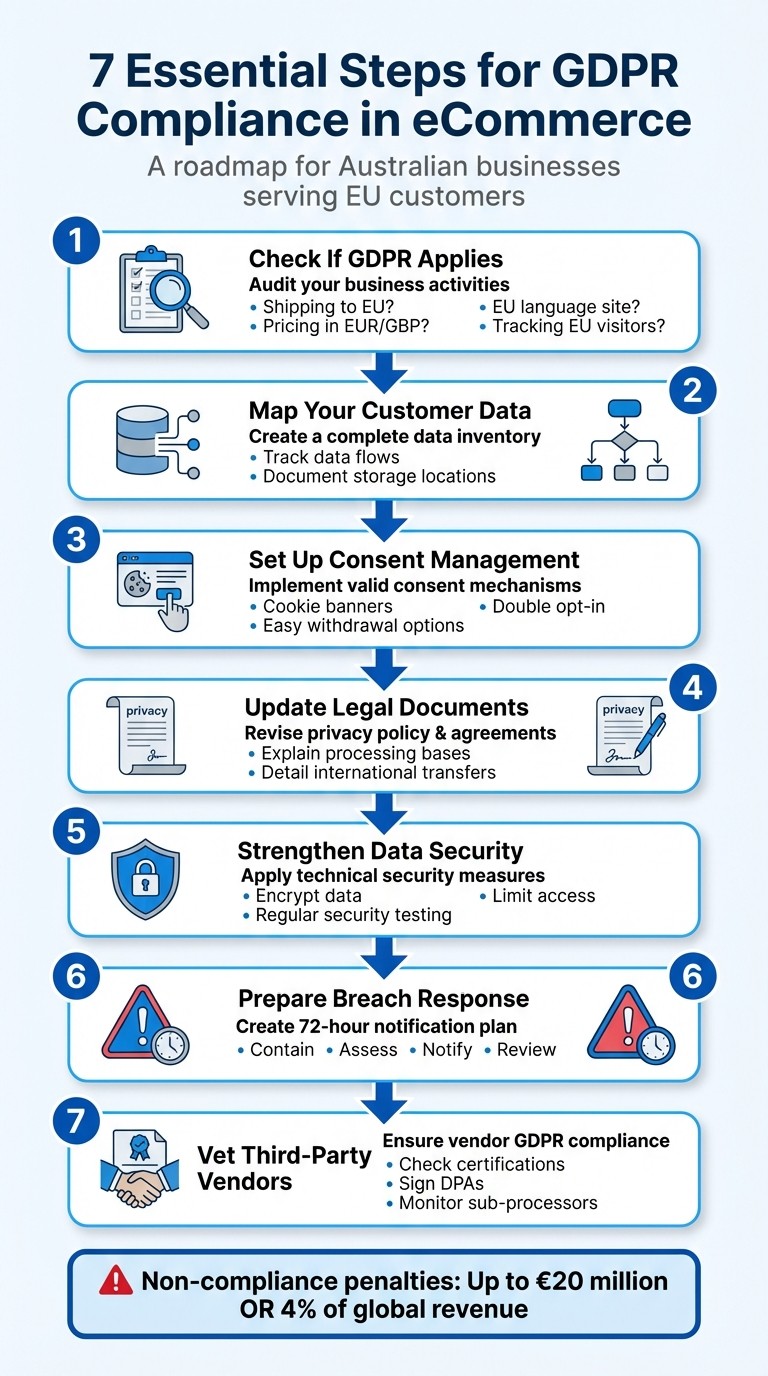
Key steps for compliance:
Audit your activities to determine if GDPR applies.
Map customer data to track what you collect, where it’s stored, and how it’s used.
Update consent mechanisms (e.g., cookie banners, opt-ins) to meet GDPR standards.
Revise your privacy policy to clearly explain data handling and user rights.
Use GDPR-compliant tools and sign Data Processing Agreements (DPAs) with vendors.
Strengthen data security measures, including encryption and access controls.
Prepare a breach response plan, including notifying authorities within 72 hours.
7 Essential Steps for GDPR Compliance in eCommerce
Check If GDPR Applies to Your Australian eCommerce Business
How GDPR Applies Beyond EU Borders
GDPR isn’t limited to businesses within the EU. If your Australian eCommerce business processes personal data from individuals physically located in the EU, the regulation applies to you. This broad reach has surprised many Australian businesses.
"This Regulation applies to the processing of personal data of data subjects who are in the Union by a controller or processor not established in the Union, where the processing activities are related to: (a) the offering of goods or services... or (b) the monitoring of their behaviour." - Article 3, GDPR
One major factor is whether you’re offering goods or services to EU residents. This could mean shipping products to EU addresses, pricing items in Euros, British Pounds, or Swiss Francs, or even presenting your website in European languages. Highlighting testimonials from EU customers may also signal that you’re targeting that market.
Another factor is tracking behaviour. If you use cookies, pixels, or analytics tools to monitor visitors from the EU - whether for ad targeting, profiling, or understanding user behaviour - you’re required to comply with GDPR, even if you’re not selling directly to EU customers.
Start by auditing your business to determine if these triggers apply to your operations.
Review Your Business Activities
Use the triggers above as a checklist when examining your business practices. For instance, look for activities like collecting email addresses from EU residents for newsletters, managing support requests from EU customers, or employing remote workers based in the EU. Each of these could create GDPR compliance obligations.
"The GDPR does not apply to occasional instances. Rather, regulators look for other clues to determine whether the organisation set out to offer goods and services to people in the EU." - Ben Wolford, Editor in Chief, GDPR.eu
If complying with GDPR isn’t feasible, you could avoid EU interactions altogether. This might involve removing EU currencies, languages, and shipping options from your website or adding disclaimers that exclude EU customers. Alternatively, tools like a Consent Management Platform can help geotarget EU visitors and display GDPR-compliant consent banners.
Lastly, keep in mind that Brexit has led to the UK implementing its own version of GDPR. If you have UK customers, you’ll need to meet UK GDPR requirements separately, although they are almost identical to the EU’s version.
2025 GDPR Compliance CHECKLIST
Map Your Customer Data and Create an Inventory
Once you've confirmed that GDPR applies to your operations, the next step is to figure out what personal data you collect and where it goes. This process, known as data mapping, helps you document the entire lifecycle of customer data - from the moment it's collected to when it's deleted or de-identified.
"Data mapping shows the journey of an organisation's data from collection to destruction or de-identification, with all the steps in between." - Jodie Siganto, Founder, Privacy 108
Building a detailed inventory of your data has multiple benefits. It speeds up customer data requests, highlights security weak spots, and avoids holding onto unnecessary information. A failure to manage data properly can have serious consequences. For example, British Airways faced a £183 million fine in 2019 after a breach compromised the data of 500,000 customers, with poor data management cited as a key issue. Knowing exactly what data you have and where it's stored makes it much easier to respond to breaches and implement strong security measures.
Find Where You Collect Personal Data
Start by identifying all the ways you collect customer information. This includes obvious sources like checkout forms and newsletter sign-ups, but also less obvious ones like Google Analytics, customer support chats, and even physical documents.
Under GDPR, "personal data" covers more than just names and email addresses. It also includes things like IP addresses, cookie identifiers, browsing history, GPS location data, and device IDs. To keep track of everything, create a spreadsheet that lists every collection point, what data is gathered, why it's collected, where it's stored (e.g., cloud services, local servers, or employee devices), and whether it's shared with third parties.
For example, a checkout form might collect names, addresses, phone numbers, payment details, and IP addresses, while newsletter sign-ups typically capture names, emails, and timestamps. Keeping a record of where each subscriber signed up can also help you maintain a clear trail of consent.
Don't forget about less obvious data sources, such as social media scraping, referral networks, automated error reports, and customer testimonials. Each of these can create compliance obligations, so they need to be included in your data map.
Track How Data Moves Through Your Systems
Once you've mapped out where data is collected, the next step is to track how it flows through your systems. This helps you uncover potential vulnerabilities. Make a list of all third-party tools you use - such as payment processors (e.g., Stripe), email platforms (e.g., Mailchimp), analytics tools (e.g., Google Analytics), and logistics partners - and ensure they comply with GDPR by having signed Data Processing Agreements (DPAs) in place.
If you're using US-based servers or software tools, document these data transfers and confirm that appropriate safeguards are in place. For instance, enabling IP anonymisation in Google Analytics can reduce the amount of identifiable personal data collected during website visits.
Also, review your data retention and deletion policies to ensure you're not keeping information longer than necessary. GDPR requires outdated customer data to be deleted regularly. Clearing out old data isn't just good practice - it’s a legal obligation.
Set Up Consent Management Systems
After organising your data inventory, the next crucial step is ensuring all your data collection methods align with GDPR consent requirements. Once you've mapped out your data, the focus shifts to collecting it legally by obtaining valid consent. This means consent must be freely given, specific, informed, and unambiguous. Users should actively opt in - like ticking an empty checkbox or clicking "Accept." Pre-ticked boxes or passive actions, such as simply browsing a site, don't meet the standard. This process bridges the gap between data mapping and compliant data collection.
It's also essential to let users opt in for specific services without forcing them to agree to unrelated terms. For instance, someone making a purchase shouldn't be required to subscribe to marketing emails. Consent requests must stand alone and cannot be bundled with other terms or conditions.
"Consent means offering individuals real choice and control. Genuine consent should put individuals in charge, build trust and engagement, and enhance your reputation." - Information Commissioner's Office
Add Cookie Banners and Consent Tools
Introduce cookie banners that block non-essential cookies until users actively click "Accept." These banners must include a clearly visible "Reject All" option, displayed with the same prominence as "Accept All." Avoid using implied consent tactics. To streamline compliance, consider tools like CookieYes, Transcend, or OneTrust. These Consent Management Platforms (CMPs) can handle cookie scanning, banner management, and consent tracking automatically.
For email marketing, implement double opt-in methods where users confirm their subscription through a verification link. This ensures their consent is genuine and traceable.
If your website serves a global audience, geotargeting tools can help display GDPR-compliant banners exclusively to visitors from the EU and the UK, while keeping a standard interface for users in other regions.
Make It Easy for Users to Withdraw Consent
Withdrawing consent should be just as straightforward as granting it. Include an easily accessible "Unsubscribe" link in every marketing email and a persistent "Cookie Settings" button or icon on your website. When users opt out, ensure your systems update immediately by syncing marketing platforms with your CRM.
For more complex requests, like the "Right to be Forgotten", verify the user's identity before taking action. Maintain detailed records of consent and withdrawal requests to demonstrate your compliance if needed. Keeping these audit trails not only ensures transparency but also helps you stay prepared for regulatory checks.
Update Your Privacy Policy and Legal Documents
Once you've set up consent mechanisms, it's time to revise your legal documents to align with GDPR's transparency standards. Your privacy policy should clearly outline how you handle data. This includes naming your data controller, providing contact details for your Data Protection Officer (DPO) (if applicable), and listing the legal bases for processing data - whether it's based on consent, contract performance, or legitimate interests.
GDPR emphasises that privacy policies must be "concise, transparent, intelligible, and easily accessible". Avoid drowning your audience in legal jargon. Instead, write as though you're explaining things in person. A layered approach works well: start with a brief summary, then link to the full policy for those who want more details.
If you're an Australian business acting as a data processor for EU clients, your Data Processing Agreements (DPAs) also need attention. These agreements must include GDPR-required clauses, such as processing data only under documented instructions and having clear breach notification procedures.
This step bridges the gap between your technical compliance efforts and the clear communication your customers expect from you.
Add Information About Data Subject Rights
Once your legal framework is updated, make sure your policy empowers users by outlining their GDPR rights. These rights include accessing their personal data, correcting inaccuracies, requesting deletion (the "right to be forgotten"), receiving data in a portable format, objecting to processing for direct marketing, and limiting how their data is used.
Clearly list these rights and provide straightforward instructions on how users can exercise them. Be sure to include details like response time frames and any applicable fees. Also, explain how users can lodge complaints with supervisory authorities, such as the UK Information Commissioner's Office.
If you use automated decision-making - for example, in credit scoring, personalised ads, or dynamic pricing - your policy should explain the logic behind these processes and how users can challenge decisions. Additionally, specify how long you retain personal data or the criteria you use to determine retention periods.
Handle International Data Transfers Properly
Tracking data flows is essential, but ensuring secure and compliant international transfers is equally important for a thorough GDPR strategy.
If you're transferring EU customer data to Australia or other non-EU countries, you'll need to implement specific safeguards. As of mid-2025, the EU has not recognised Australia as having "adequate" data protection. This means data can't be transferred across borders without additional measures. Your privacy policy should clearly state where data is transferred and describe the protections in place.
For international transfers, list all destinations and apply safeguards like Standard Contractual Clauses (SCCs). These are pre-approved terms provided by the European Commission. In 2019, 88% of organisations used SCCs as their main transfer mechanism. SCCs come in modular formats tailored to different scenarios: Controller-to-Controller, Controller-to-Processor, Processor-to-Processor, and Processor-to-Controller.
After the Schrems II ruling, it's also necessary to conduct a Transfer Impact Assessment (TIA) to ensure the destination country's laws offer protections equivalent to those in the EU. Document your findings and use supplementary measures, such as end-to-end encryption. Update all vendor agreements to include the 2021 SCCs, as older agreements needed to be revised by the 27 December 2022 deadline. For data involving UK customers, use the UK International Data Transfer Agreement or the UK Addendum to the EU SCCs.
Improve Data Security and Prepare for Breaches
Protecting customer data is about more than just ticking compliance boxes - it’s about avoiding the financial and reputational fallout from breaches. In 2024, the global average cost of a data breach hit $4.88 million, marking a 10% increase from the previous year. For Australian eCommerce businesses dealing with EU customer data, the stakes are especially high. Strong security measures are not just advisable - they’re essential.
Under GDPR Article 32, businesses are required to implement "appropriate technical and organisational measures to ensure a level of security appropriate to the risk, including inter alia as appropriate: the pseudonymisation and encryption of personal data". This means your security efforts must align with the sensitivity of the data you handle and the potential impact of a breach. A solid security framework also strengthens your overall GDPR compliance.
Apply Core Security Measures
Once you’ve mapped your data and set up consent protocols, the next step is to ensure robust protections are in place.
Encrypt data in transit and at rest. Use HTTPS with SSL/TLS certificates to secure data moving between your site and customers. For stored data, full disk encryption is a must, and you might also consider file-level encryption for particularly sensitive information. Partner with PCI DSS-compliant processors that tokenise and encrypt payment data.
Enforce least privilege for data access. Limit employee access to only the data they genuinely need. Enable multi-factor authentication (MFA) on all user accounts, especially those with administrative privileges. Use separate credentials for accessing and managing backups to minimise damage in case of a breach.
Purge unnecessary customer data regularly. Collect only the data you truly need. For example, if a phone number isn’t required for delivery, don’t ask for it. The less data you retain, the smaller the impact if a breach occurs.
GDPR also mandates regular testing of your security measures. Set up processes to routinely test, assess, and evaluate the effectiveness of your protections. This includes running breach simulations so your team knows how to escalate issues and respond effectively.
Set Up Data Breach Notification Procedures
Even with strong preventive measures, a quick and effective response to breaches is critical.
GDPR requires data controllers to notify the relevant supervisory authority within 72 hours of becoming aware of a personal data breach - unless it’s unlikely to pose a risk to individuals’ rights and freedoms. Notifications must include details like the nature of the breach, the categories and approximate number of affected individuals and records, the Data Protection Officer’s contact information (if applicable), potential consequences, and the steps taken to mitigate harm.
Create a written breach response plan that outlines clear roles and steps. Your response team should include a leader, ICT/forensics experts, legal counsel, and a privacy officer, all empowered to act immediately without needing further approval.
A breach response typically involves four steps:
Contain the breach to prevent further damage.
Assess the type of data involved and the potential risks.
Notify the supervisory authority and affected individuals, if required.
Review the incident to identify lessons and update security policies.
If a breach poses a high risk to individuals’ rights and freedoms, you must notify those affected without undue delay. However, if the data was encrypted or otherwise rendered unreadable to unauthorised parties, individual notification may not be necessary.
Document every breach, even those that don’t require reporting. Records should include the facts, effects, and remedial actions taken. This documentation not only demonstrates compliance but also helps authorities verify your adherence to GDPR requirements. Additionally, ensure your Data Processing Agreements with third-party providers include clauses obligating them to notify you immediately in case of a breach.
Choose GDPR-Compliant Third-Party Tools and Partners
If your eCommerce business relies on third-party tools to process customer data, you're not off the hook when it comes to GDPR compliance. Under the regulation, you're still responsible for any non-compliance by these vendors. This means every tool or service that interacts with customer data makes you accountable for ensuring it meets GDPR standards.
And the stakes? They're massive. Since January 2022, GDPR violations have racked up around $1.74 billion in penalties. For instance, in September 2025, France's data protection authority (CNIL) fined SHEIN €150 million for using tracking cookies without proper consent. These examples highlight why carefully vetting your vendors isn’t just a box-ticking exercise - it’s a critical part of managing your risk and maintaining compliance. This process ties directly into your broader GDPR strategy, ensuring that every partner handling EU customer data is held to the same high standards.
Check Vendor Compliance Status
Start by thoroughly assessing each vendor's compliance credentials. Before signing on with any third-party service, demand solid proof of their GDPR readiness. This could include certifications like ISO 27001 or audit reports such as SOC 1, 2, and 3. Also, check if they provide standard Data Processing Agreements (DPAs) on their websites.
Ask for detailed documentation about how they store data, their access controls, and how they manage international data transfers - especially since Australia is considered a "non-adequate" country under GDPR. Ensure they use robust security measures like encryption, pseudonymisation, and strict access controls. Additionally, confirm they have a process in place to notify you immediately in the event of a data breach, so you can meet the 72-hour reporting deadline.
To stay organised and demonstrate your due diligence to regulators, maintain a transparency spreadsheet. Track all your third-party processors, their compliance status, whether a DPA is signed, and if data crosses international borders. This record becomes an integral part of your overall GDPR risk management framework.
Update Data Processing Agreements with Vendors
A Data Processing Agreement (DPA) is your safety net, ensuring vendors handle data in line with GDPR. These agreements must include specific clauses outlined in Article 28. For instance, processors are required to act only on your documented instructions, ensure their staff are bound by confidentiality, and avoid engaging sub-processors without your written approval.
"Processing by a processor shall be governed by a contract... that sets out the subject-matter and duration of the processing, the nature and purpose of the processing, the type of personal data and categories of data subjects and the obligations and rights of the controller." – GDPR Article 28
Customise each DPA to fit your specific needs. Clearly outline the types of data being processed, the duration, and the purpose. Require vendors to assist in fulfilling data subject rights, notify you immediately of any breaches, and either delete or return data once the contract ends. If data will be transferred outside the European Economic Area, make sure the agreement includes Standard Contractual Clauses or another valid mechanism.
Avoid relying on generic DPA templates. Tailor them to your operations, specifying the exact data types and processing activities involved. Non-compliance with Article 28 can result in fines of up to €10 million or 2% of your global annual revenue, whichever is greater. Additionally, keep an up-to-date list of each vendor’s approved sub-processors to maintain transparency throughout your supply chain. This level of oversight complements your earlier data mapping and consent management efforts, creating a well-rounded compliance framework.
Conclusion
Meeting GDPR compliance isn’t something you check off a list - it’s an ongoing responsibility. As Kevin Yun from ComplyDog explains:
"GDPR compliance is an ongoing process, not a one-time effort".
With data protection laws, security threats, and business operations constantly shifting, your compliance framework needs to evolve alongside them.
Staying compliant isn't just about avoiding hefty fines - it’s about building trust. Considering that 86% of consumers are concerned about how companies handle their data, demonstrating accountability can strengthen customer confidence. Plus, it enhances security, reducing the risk of breaches. Measures like encryption and access controls don’t just protect your business - they safeguard your customers too.
To stay ahead, establish a proactive compliance routine. Conduct regular audits to keep your data inventory up to date, ensure third-party vendors meet compliance standards, and clear out obsolete data. When adopting new tools or changing how you process data, update your privacy policy immediately. Regular staff training is also crucial, helping your team recognise and counter threats like phishing. These steps, combined with the strategies outlined earlier, will help you maintain a strong and effective GDPR compliance framework.
FAQs
Does GDPR apply to Australian eCommerce businesses?
Australian eCommerce businesses need to comply with GDPR if they:
Handle personal data of individuals located in the EU or UK.
Operate a physical location or have an established presence in the EU.
Sell or provide goods or services to EU customers, regardless of whether they charge for them.
Track or analyse the behaviour of EU individuals, such as using cookies or running targeted ads.
Even if your business is based outside the EU, meeting any of these criteria means GDPR compliance isn't optional. Getting familiar with these rules is essential to avoid fines and build trust with international customers.
What are the key steps for GDPR compliance when mapping personal data?
To align with GDPR requirements, begin with a thorough data audit. Pinpoint every piece of personal data your business gathers - where it comes from, where it’s stored, and how it’s utilised. Make sure to document data flows, including any sharing with third parties, and create a clear map of all processing activities. Keep this documentation up to date by reviewing it regularly to account for any changes in your operations. Taking these steps ensures you safeguard customer privacy while staying compliant.
What steps should businesses take to manage international data transfers under GDPR?
Under the General Data Protection Regulation (GDPR), businesses can only transfer personal data outside the European Economic Area (EEA) if they meet certain conditions. This might involve relying on an EU adequacy decision, implementing safeguards like Standard Contractual Clauses or Binding Corporate Rules, or using another approved method. In some instances, specific derogations might also apply.
Businesses must also keep thorough records of all data transfers and, when necessary, carry out a transfer impact assessment. These measures not only ensure compliance but also help safeguard personal data and build customer confidence in cross-border dealings.



